Lab: Username Enumeration via Subtly Different Responses
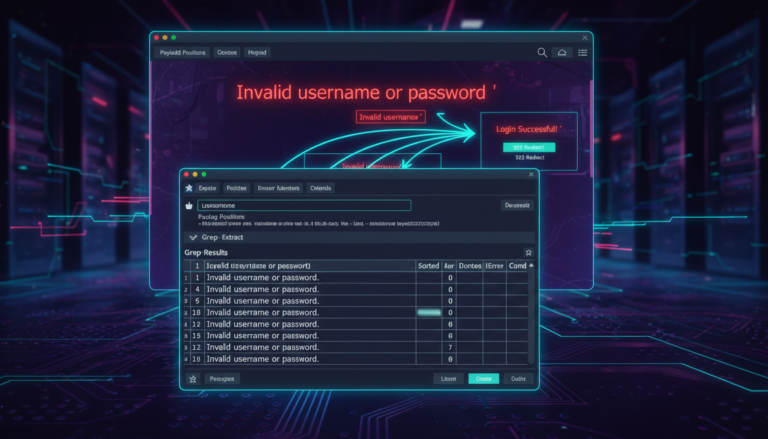
Introduction: Username enumeration vulnerabilities can manifest in increasingly sophisticated ways as developers attempt to mitigate basic enumeration techniques. This lab demonstrates how even minute differences in application responses—such as a single character variation—can be exploited to identify valid user accounts. Such subtle distinctions require more advanced…