The old way of thinking was simple: protect the “perimeter” with a firewall and you were safe. But in 2026, the perimeter has dissolved. With the rise of hybrid work and the explosion of smart devices, the Endpoint is now the primary battlefield.
An endpoint is any device that communicates with your business network. In Nigeria today, this includes not just company laptops, but also the personal smartphones used for WhatsApp Business and the smart surveillance systems monitoring your physical storefronts.
1. The 2026 Definition of an “Endpoint”
If it has an IP address and connects to your data, it’s an endpoint. In a modern Nigerian enterprise, you must account for:
- The Mobile Workforce: Smartphones and tablets running banking and inventory apps.
- IoT & Smart Infrastructure: Connected CCTV cameras, smart power meters, and IoT sensors in agricultural or manufacturing hubs.
- Cloud Terminals: Laptops accessing your Next.js dashboards and Prisma-backed databases.
2. From Antivirus to XDR: The Tech Evolution
In 2026, standard antivirus software is about as effective as a wooden gate against a bulldozer. Modern threats use “living-off-the-land” techniques that don’t use traditional files, making them invisible to old-school scans.
The Shift to EDR and XDR
To stay protected, businesses have moved to Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR). These systems don’t just look for “bad files”; they look for “bad behavior.”
- EDR: Monitors the activity on a single device. If a laptop suddenly tries to encrypt 1,000 files in a minute, the EDR kills the process instantly.
- XDR: Connects the dots across your entire network. If a suspicious login happens in Kano and two minutes later a database in Lagos begins an unusual export, the XDR recognizes the correlation and shuts down the identity.
Pro-Tip: For technical teams, ensuring your EDR/XDR is integrated with your CI/CD pipeline prevents compromised code from ever reaching production.

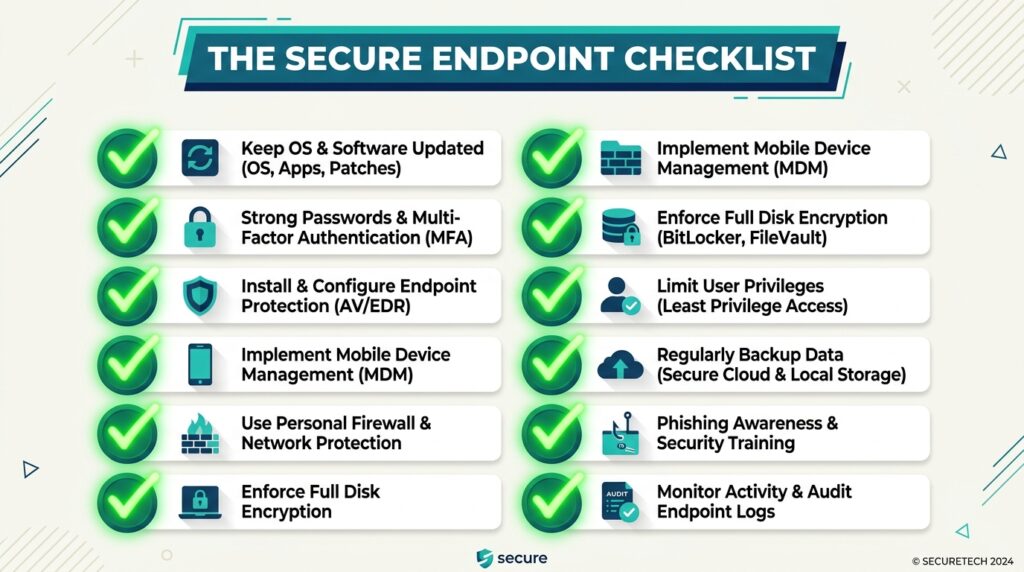
3. Three Non-Negotiable Rules for 2026
I. Zero Trust “Always Verify”
Assume every device is already compromised. Before a device can access your network, it must pass a “Health Check”:
- Is the OS updated?
- Is the disk encrypted?
- Is the user using a FIDO2 Hardware Key?
II. Secure the “Things” (IoT Security)
Smart surveillance and IoT devices are often the weakest links. They frequently ship with default passwords like admin:admin.
- Action: Place all IoT devices (CCTV, Smart Sensors) on a separate, isolated VLAN. Even if a camera is hacked, the attacker cannot “jump” to your financial records.
III. Automated Patching
In 2026, “I’ll update it tomorrow” is a death sentence. Vulnerabilities are exploited by AI-driven bots within minutes of being discovered. Your endpoint strategy must include Automated Patch Management to ensure every device is running the latest security headers.
2026 Endpoint Security Comparison
| Feature | Legacy Antivirus | Modern EDR/XDR |
| Detection Basis | Known Signatures | AI Behavioral Patterns |
| Response | Delete File | Isolate Host / Revoke Tokens |
| Speed | Reactive (Slow) | Autonomous (Milliseconds) |
| Coverage | Windows/Mac only | Mobile, IoT, Cloud, Linux |
The 5-Minute Network Audit
To align with this week’s theme of Action, perform this quick audit of your business network today:
- Ghost Hunt: Use a network scanner to identify every device currently connected. Is there a device you don’t recognize?
- Password Purge: Ensure no connected hardware (routers, cameras) is using factory-default credentials.
- MDM Check: If employees use personal phones for work, ensure you have a Mobile Device Management (MDM) solution to wipe business data if the phone is lost.
- Inactivity Kill-Switch: Set all sessions to auto-terminate after 30 minutes of inactivity to prevent physical “walk-up” exploits.
The Takeaway
Your network’s strength is not determined by your most expensive firewall, but by the most neglected smartphone connected to your Wi-Fi. In 2026, endpoint security is about visibility and machine-speed response.