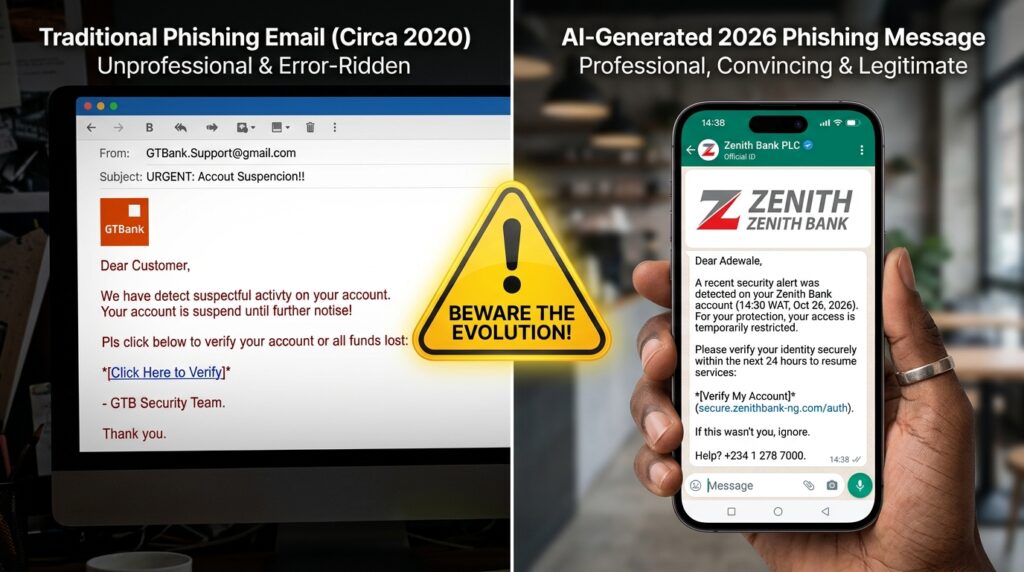
In 2026, phishing has graduated from “Nigerian Prince” emails to Agentic AI deception. According to recent 2026 outlooks, Nigeria ranks as the third most targeted country in Africa for phishing. The threats have moved beyond your inbox and into your WhatsApp, your LinkedIn DMs, and even your voice calls through AI-generated “vishing.”
Building a phishing-resistant team is no longer a “one-off” seminar; it is a continuous operational protocol.
1. Recognize the 2026 Threat Landscape
The “red flags” we taught in 2022 poor grammar and weird email addresses are largely gone. AI now handles the spelling and the tone.
- The WhatsApp Pivot: Scammers are increasingly impersonating government officials (like PenCom or NITDA) on WhatsApp, offering “relief packages” or “job opportunities” to trick staff into sharing BVNs or login tokens.
- Deepfake Vishing: We are seeing attacks where a “Manager” calls a junior accountant. The voice is a perfect AI clone of the manager, requesting an “urgent” transfer to a new vendor.
- The “Identity” Target: Attacks are no longer just about malware; they are about stealing Identity Tokens to bypass Multi-Factor Authentication (MFA).
2. Step-by-Step: Building the “Human Firewall”
To meet NITDA’s 2026 Information Security Objectives, organizations should aim for an 80% pass rate on internal awareness exercises.
Step A: Implement “Vibe-Check” Protocols
Create a company-wide rule: Any request for money, credentials, or sensitive data made via a messaging app (WhatsApp/Slack) must be verified through a second, “out-of-band” channel—like a direct phone call or a face-to-face confirmation.
Step B: Gamified Phishing Simulations
Don’t just lecture; simulate. Use AI tools to send “safe” phishing tests to your team.
- The Metric: Calculate your Resilience Score (Rs):
-
- Treported: Number of staff who reported the test.
- Tclicked: Number of staff who clicked the link.
- High resilience means your team is actively “hunting” threats, not just avoiding them.
-
Step C: The “No-Blame” Reporting Culture
If an employee clicks a suspicious link, they shouldn’t fear for their job. If they fear punishment, they will hide the mistake, giving the hacker more time to lateralize. Reward the “Quick Report” instead of punishing the “Slow Click.”

3. Technical Backstops: Phishing-Resistant MFA
You cannot rely on the “Human Layer” alone. In 2026, the only truly phishing-resistant defense is Hardware-Backed Identity.
- Ditch SMS MFA: SMS codes are easily intercepted or “sim-swapped” in Nigeria.
- Adopt FIDO2/Passkeys: Move your privileged accounts (Admin, Finance, IT) to physical security keys. These cannot be phished because they require physical presence and a cryptographic handshake that a fake website cannot replicate.
- Conditional Access: Set up your systems to only allow logins from “Compliant” devices located within Nigeria (or specific GEO-fenced areas).

The Takeaway
In the Nigerian business context, your team is your greatest asset and your biggest potential vulnerability. By moving from “Awareness” to “Active Protocol,” you turn every employee into a sensor on your network.