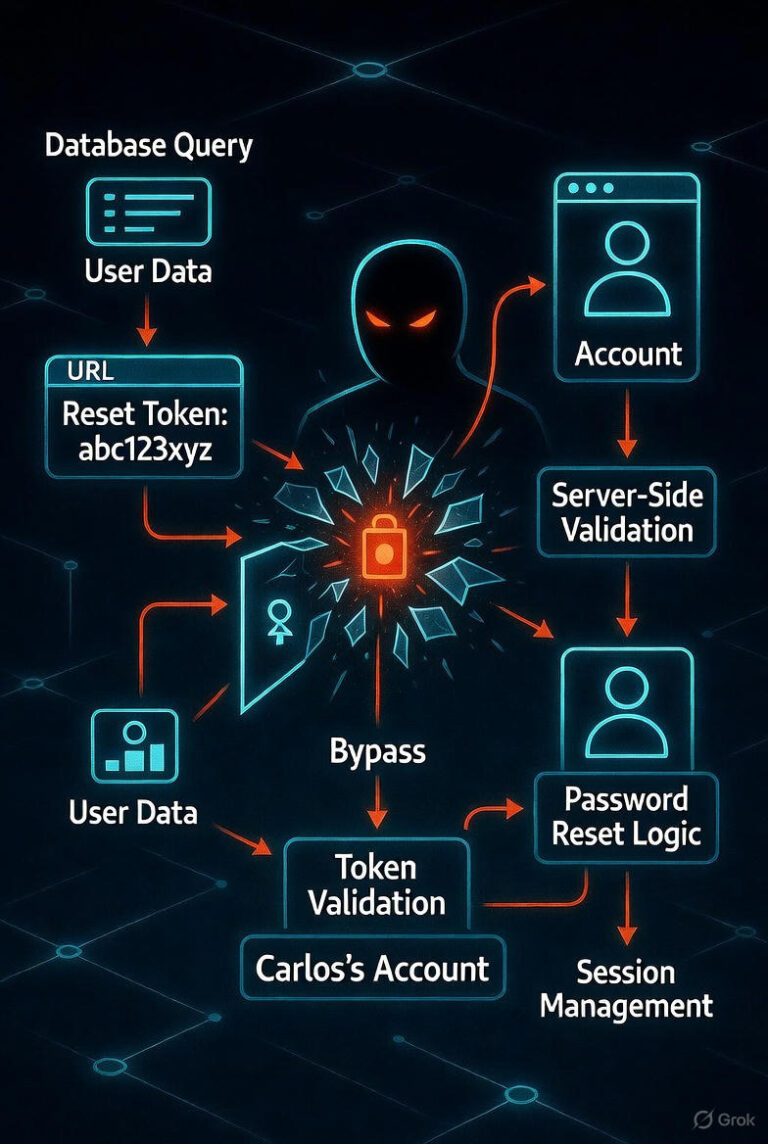
Lab: Password Reset Broken Logic

Introduction: Password reset mechanisms serve as critical recovery pathways for users who…

Introduction: Password reset mechanisms serve as critical recovery pathways for users who…
Introduction: Timing-based vulnerabilities represent a sophisticated class of side-channel attacks that exploit variations in…

Introduction: Password reset mechanisms serve as critical recovery pathways for users who…
PortSwigger Lab: 2FA Simple Bypass Introduction: Two-factor authentication (2FA) serves as a critical…

Introduction: The “Blind OS Command Injection with Time Delays” lab, part of…

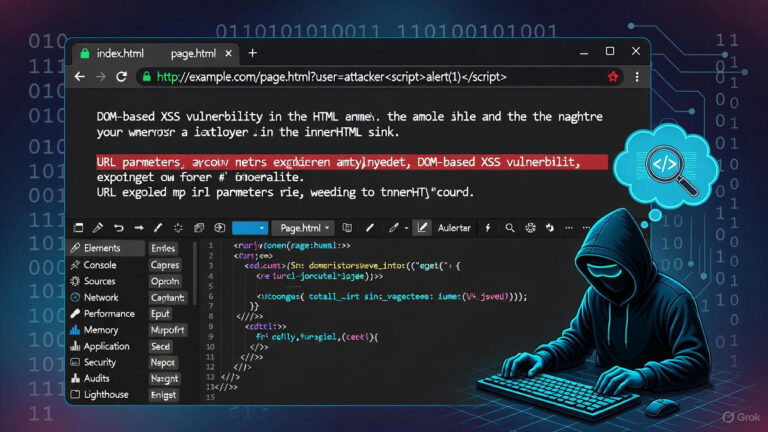
Introduction: The PortSwigger Web Security Academy provides guided labs where security professionals can practice identifying and…

Introduction: This lab demonstrates a Reflected Cross-Site Scripting (XSS) vulnerability where user input is…