Lab: Reflected XSS into HTML Context with Nothing Encoded
Vulnerability Type: Reflected Cross-Site Scripting (XSS) Attack Vector The vulnerable application reflects…
Vulnerability Type: Reflected Cross-Site Scripting (XSS) Attack Vector The vulnerable application reflects…
Vulnerability Type: Stored Cross-Site Scripting (XSS) Attack Vector The vulnerable application stores…
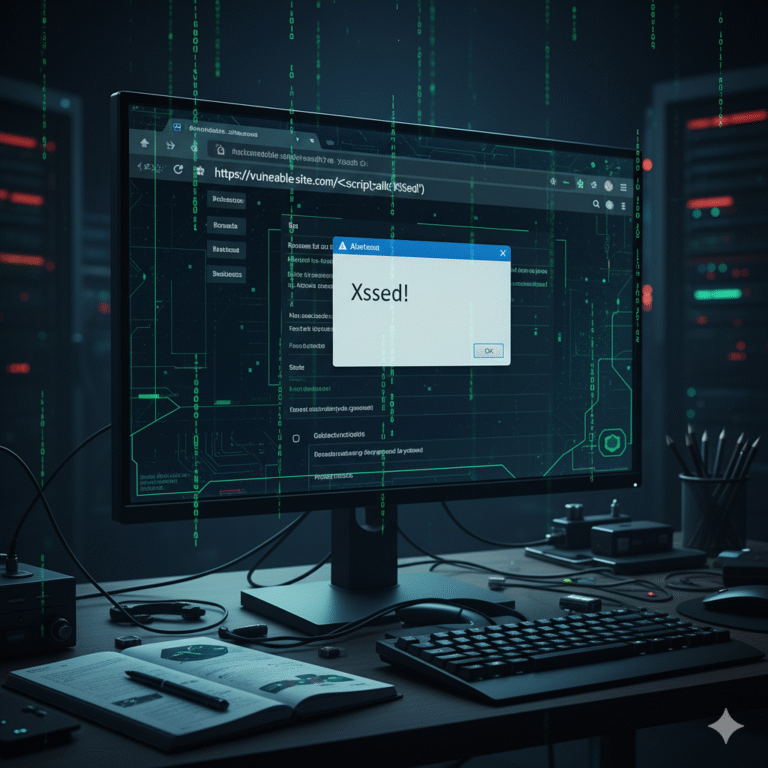
Methodology Conclusion This lab highlights how a simple marker string can reveal…

Attack Vector Used Exploitation Steps Mitigation Strategies Conclusion This lab demonstrates how…

Attack Vector Used Exploitation Steps Mitigation Strategies Conclusion This lab demonstrates how…
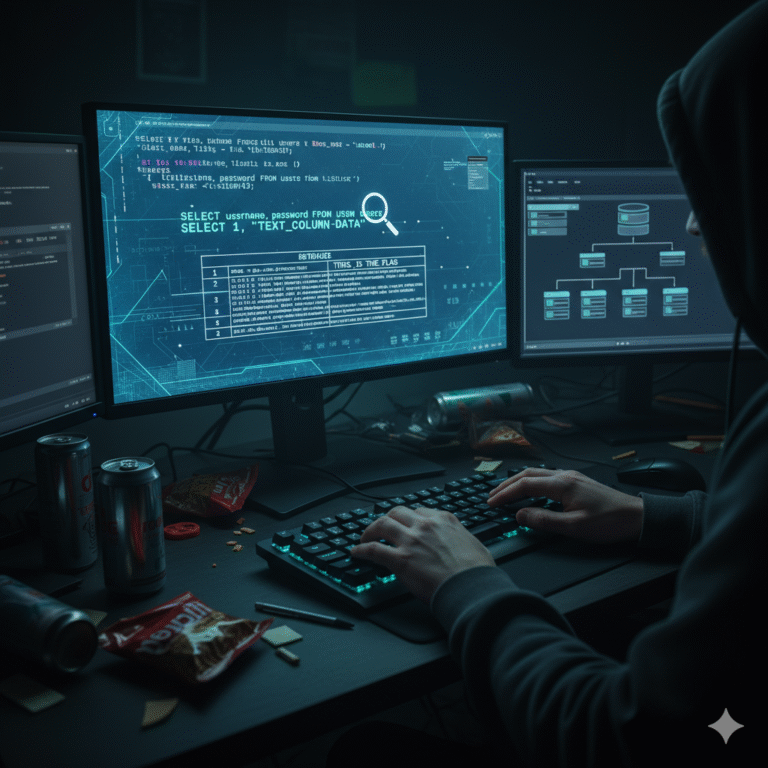
Introduction Lab 8 demonstrates a UNION-based SQL injection technique to identify which…

Introduction Lab 7 demonstrates a practical UNION-based SQL injection technique to determine…